.jpg)
Email Deliverability Best Practices: The Ultimate Guide for High-Volume Senders
Achieving consistent inbox placement is the single greatest determinant of your marketing ROI, yet for high-volume senders, this goal requires diligent practice and technical mastery.
This comprehensive guide breaks down exactly what you need to do to keep your messages out of the spam folder, covering everything from establishing foundational technical authentication like SPF, DKIM, and DMARC, to the rigorous database maintenance and content hygiene necessary to satisfy modern spam filters.
You will learn how to benchmark your performance, strategically choose between dedicated versus shared resources, and implement compliance standards like double opt-in to build long-term trust with recipients and Internet Service Providers (ISPs).
By implementing these essential strategies, you transform your sending from a reactive risk into a predictable, high-performing communication channel.
Understanding Email Deliverability Fundamentals
Mastering email deliverability best practices begins with a clear understanding of what happens after you hit "send." While many marketers use the terms "delivery" and "deliverability" interchangeably, they represent two very different stages of the email journey. To scale successfully, you must optimize for both.
Defining Email Deliverability vs. Delivery
Email delivery is a binary technical measurement: did the recipient's mail server accept your message? If the server provides a "250 OK" response, the email is considered delivered. This stage is primarily influenced by your email infrastructure and the validity of your recipient list.
Email deliverability, or inbox placement, is the actual goal. It measures whether that accepted message landed in the primary inbox or was diverted to the spam folder. High delivery rates mean nothing if your messages are hidden where users never see them.
What Constitutes a 'Good' Deliverability Rate?
A "good" rate varies by industry, but top-tier senders generally aim for a delivery rate of 98% or higher. However, your inbox placement (deliverability) is more nuanced. For high-volume senders, maintaining an inbox placement rate above 85-90% is considered the gold standard for healthy domain reputation.
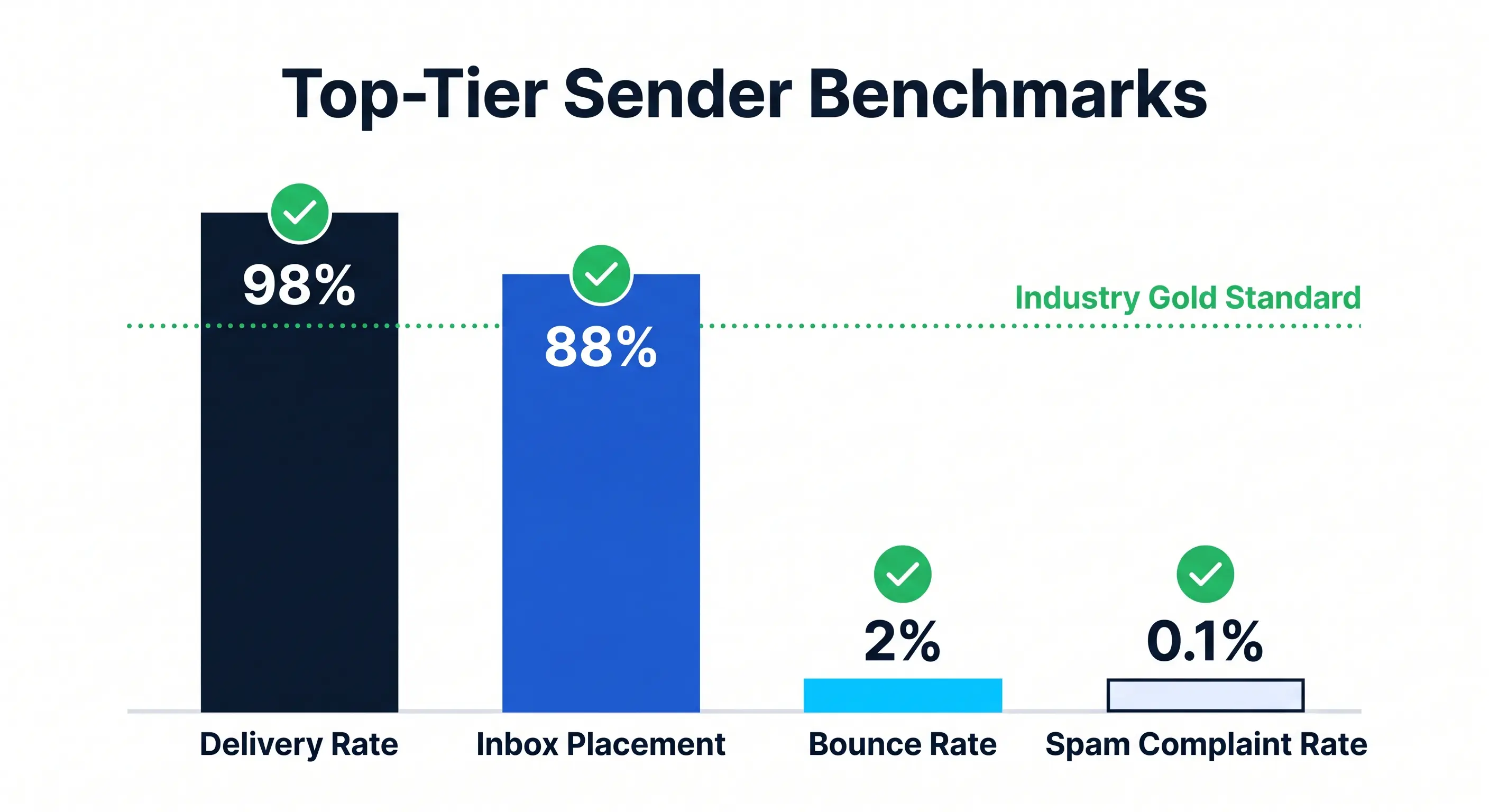
Consistently falling below these benchmarks often indicates underlying issues with your sender reputation or technical setup. Monitoring these metrics daily allows you to catch shifts in ISP (Internet Service Provider) filtering before they impact your overall ROI.
Identifying Spam Folder Placement Issues
Identifying if you have a deliverability problem can be difficult because most Email Service Providers (ESPs) report "Delivered" even if the mail went to spam. One of the first signs of a placement issue is a sudden, unexplained drop in open rates across specific providers like Gmail or Outlook.
To diagnose these issues, you should use seed list testing and monitor your Google Postmaster Tools data. If your emails are consistently bypassing the inbox, it is often due to "grey-listing" or content-based triggers that signal to ISPs your mail is unsolicited or low-value.
Using a dedicated deliverability platform helps isolate these variables by providing dedicated IPs. This ensures that your reputation isn't damaged by the "noisy neighbors" typically found on shared sending infrastructures.
Technical Authentication and Sender Reputation
Technical authentication is no longer optional; it is the foundation of email deliverability best practices. Without proper protocols, ISPs like Gmail and Yahoo have no way of verifying that you are who you say you are, leading to immediate filtering or rejection.
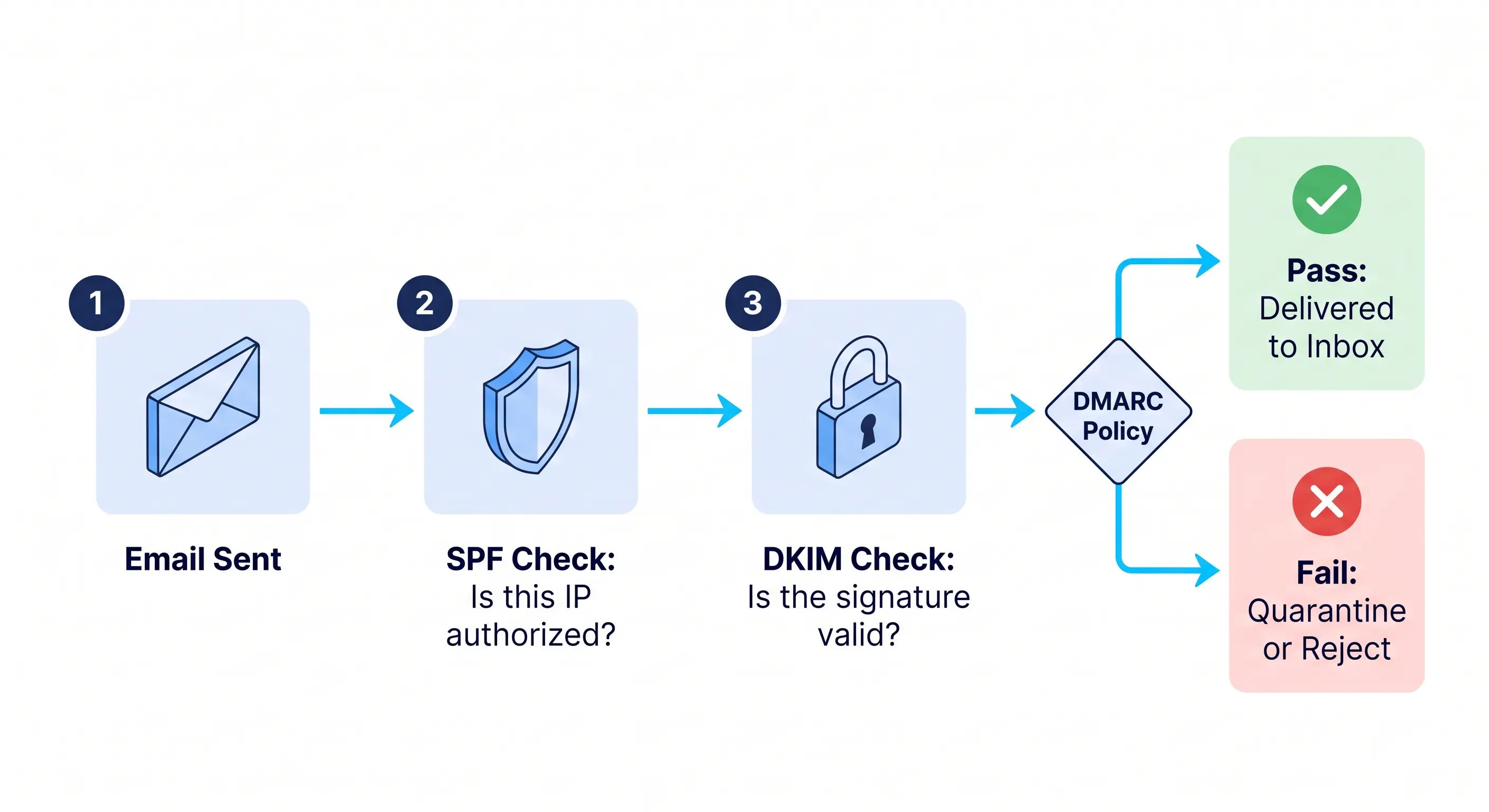
The Pillars of Email Authentication: SPF, DKIM, and DMARC
To meet the Gmail and Yahoo Sender Requirements, you must implement a "triple threat" of authentication protocols. These records reside in your DNS (Domain Name System) and act as a digital passport for your outgoing mail.
Authentication Setup Checklist:
- SPF (Sender Policy Framework):
- [ ] Create a TXT record that identifies which IP addresses and domains are authorized to send email on your behalf.
- [ ] Ensure you have only one SPF record per domain.
- [ ] Keep the record under the 10-lookup limit to avoid "permerrors."
- DKIM (DomainKeys Identified Mail):
- [ ] Generate a public/private key pair.
- [ ] Add the public key to your DNS as a TXT record.
- [ ] Use 2048-bit encryption keys for maximum security (1024-bit is increasingly considered weak).
- [ ] Verify that your email service provider is correctly "signing" every outgoing message with the private key.
- DMARC (Domain-based Message Authentication, Reporting, and Conformance):
- [ ] Set up a DMARC record that references your SPF and DKIM status.
- [ ] Start with a policy of p=none to monitor traffic without affecting delivery.
- [ ] Move to p=quarantine or p=reject once you have verified all legitimate mail sources.
- [ ] Define an rua tag to receive aggregate reports on who is sending mail using your domain.
For high-volume senders, managing these records manually across multiple domains can lead to errors. Utilizing automated domain management can significantly reduce the risk of technical failures that trigger spam filters.
Leveraging ISP Feedback Loops (FBLs)
A Feedback Loop (FBL) is a service provided by major ISPs (such as Yahoo, Microsoft, and various cable providers) that notifies the sender when a recipient marks an email as spam.
- Why FBLs Matter: They provide a direct signal from the user to the sender. If you ignore these signals, your sender reputation will plummet.
- Immediate Action: When you receive an FBL report, you must immediately suppress that recipient from your mailing list.
- Scannable Benefits:
- Reduces future complaint rates.
- Improves overall domain health.
- Helps identify specific campaigns that may be triggering negative reactions.
While Gmail does not offer a traditional FBL like other providers, they provide the Google Postmaster Tools, which offers similar insights into spam rates and authentication health.
How Technical Setup Impacts Brand Trust
Technical authentication does more than just bypass filters; it protects your brand equity. In an era of rampant phishing and "spoofing," a secure setup ensures that bad actors cannot use your domain to scam your customers.
- BIMI (Brand Indicators for Message Identification): This is the next level of technical setup. By having a strong DMARC "reject" policy, you can display your verified brand logo in the recipient's inbox, which has been shown to increase open rates and trust.
- Alignment: Ensure your "From" header domain matches the domain used in your SPF and DKIM records. This identifier alignment is critical for passing DMARC checks.
- Spam Filter Scoring: Technical errors are often the first thing filters check. You can learn more about how spam filters grade your emails to understand the weight assigned to technical versus content-based signals.
By treating your technical infrastructure as a priority rather than an afterthought, you build a resilient sending environment capable of handling high-volume outreach without the risk of being blacklisted.
Infrastructure Strategy: Dedicated vs. Shared Resources
Your email infrastructure is the foundation upon which your sender reputation is built. For high-volume senders, the choice between shared and dedicated resources isn't just a matter of cost—it is a strategic decision that determines whether your messages reach the inbox or get swallowed by spam filters.
Choosing Between Dedicated and Shared IP Addresses
A shared IP address is used by multiple organizations simultaneously. While cost-effective for low-volume senders, it introduces the "bad neighbor" effect: if another company on your IP sends spam, your deliverability suffers regardless of your own practices.
A dedicated IP address, conversely, provides exclusive control over your reputation. Mission Inbox prioritizes this isolation, offering dedicated IPs to ensure your sending score is never compromised by external actors.
When to Migrate to a Dedicated IP:
High-volume senders should transition to a dedicated IP based on these fact-based thresholds:
- Volume Consistency: If you consistently send more than 50,000 to 100,000 emails per month, a dedicated IP becomes a necessity to maintain a stable reputation.
- Reputation Control: When you need to troubleshoot deliverability issues with precision, a dedicated IP allows you to pinpoint exactly which campaigns are affecting your metrics.
- ISP Requirements: Major providers like Gmail and Yahoo look for consistent sending patterns. If your volume is high enough to generate its own "reputation footprint," staying on a shared IP often results in throttled delivery.
Domain Selection: Primary vs. Subdomains
Protecting your primary corporate domain (e.g., company.com) is critical. If your primary domain’s reputation is damaged by a high-volume marketing campaign, your internal employee emails may also fail to deliver.
To mitigate this risk, implement a subdomain strategy:
- Marketing Traffic: Use news.company.com or offers.company.com.
- Transactional Traffic: Use app.company.com or receipts.company.com.
- Cold Outreach: Use a completely separate but "look-alike" domain to ensure your main business operations remain unaffected by higher bounce rates.
Using subdomains allows you to isolate the "blast radius" of any potential deliverability issues. Each subdomain builds its own reputation, and while ISPs do associate them with the root domain, they provide a necessary layer of protection for your core business communications. You can learn more about managing these signals in our guide on monitoring domain reputation.
Managing Sending Limits and Volume Spikes
ISPs are highly sensitive to sudden fluctuations in email volume. A massive spike in traffic from an IP that usually sends very little is a classic hallmark of a compromised server or a spam bot.
Best Practices for Managing Volume:
- IP Warming: Never send 100,000 emails on day one of a new dedicated IP. You must gradually "warm" the IP over 4–6 weeks, starting with a few hundred emails and increasing the volume by 20%–30% each day.
- Pacing and Throttling: Rather than "blasting" your entire list at once, spread your sends over several hours. This prevents hitting the hourly rate limits imposed by providers like Outlook and Gmail.
- Handling Spikes: If you have a major seasonal promotion (e.g., Black Friday), begin increasing your daily volume weeks in advance. This "pre-warming" signals to ISPs that the upcoming high volume is expected and legitimate.

By treating your infrastructure as a controlled environment, you remove the variables that lead to unpredictable deliverability. Whether through dedicated IPs or segmented domain strategies, the goal is total control over the signals you send to receiving mail servers.
List Hygiene and Database Maintenance Strategies
Maintaining a clean email list is the foundation of email deliverability best practices. Even if your infrastructure is perfect, sending messages to invalid or uninterested recipients will eventually damage your sender reputation. High bounce rates and low engagement tell Inbox Service Providers (ISPs) that you aren’t managing your data responsibly, which can lead to your emails being filtered into the spam folder.
Cleaning Your List: A Step-by-Step Approach
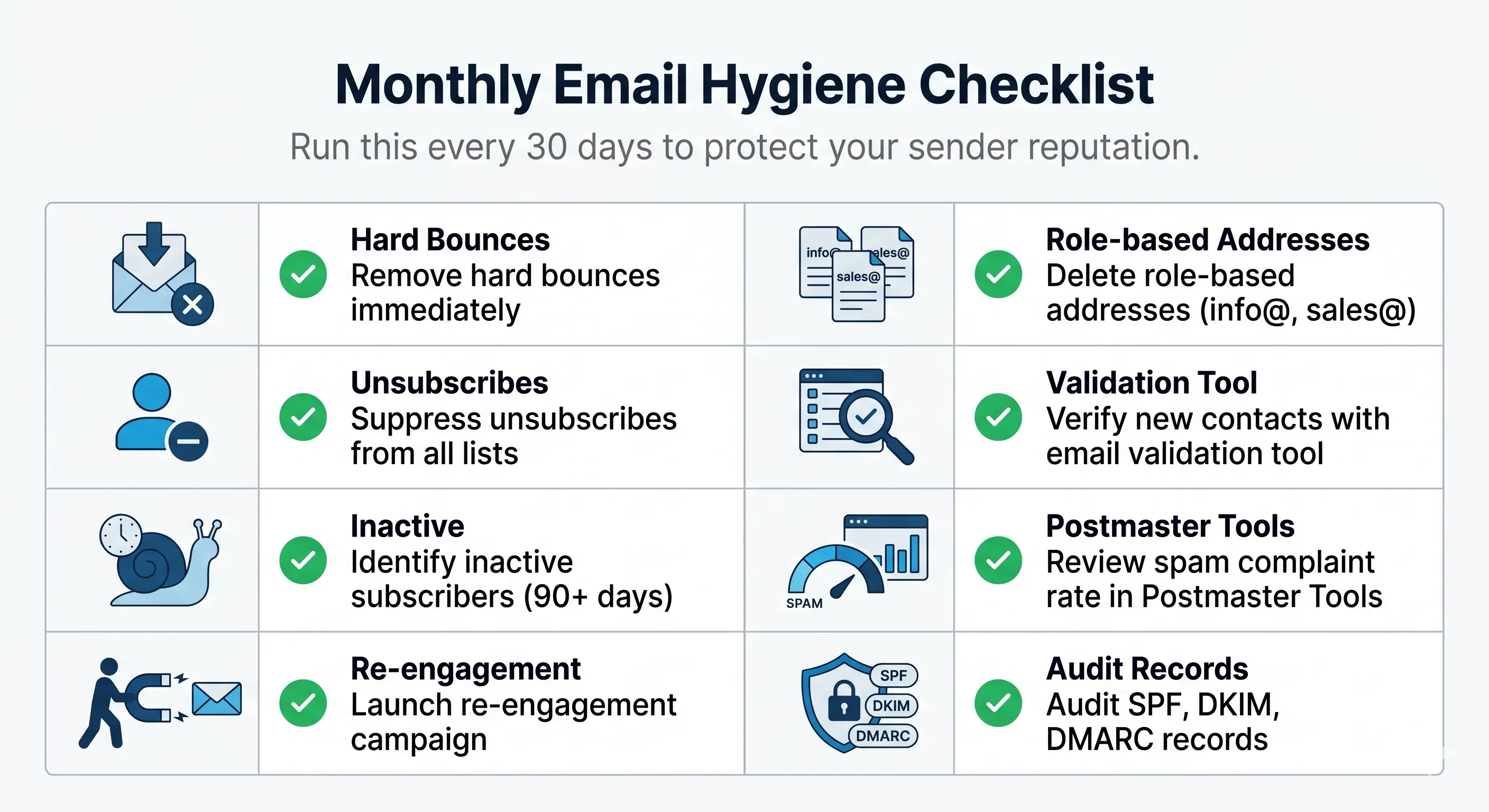
Regularly "scrubbing" your list ensures you are only reaching people who want to hear from you. Follow these instructional steps to keep your database healthy:
- Identify Inactive Subscribers: Define what "inactive" means for your business. Typically, this is anyone who hasn’t opened or clicked an email in the last 3–6 months.
- Launch a Re-engagement Campaign: Send a final, high-value "Win-back" email to your inactive segment. Ask them if they still want to receive your updates.
- Implement a Sunset Policy: If subscribers do not engage with your re-engagement campaign, remove them immediately. Continuing to mail unengaged users is a primary cause of declining domain reputation.
- Remove Role-Based Addresses: Delete emails starting with info@, support@, or sales@ if they are part of a marketing list. These are often managed by multiple people and lead to higher complaint rates.
- Audit Your Opt-in Source: Ensure every contact on your list arrived via a clear opt-in process. Purchased lists are a violation of most service terms and a guaranteed way to hit spam traps (email addresses used by ISPs specifically to catch unauthorized senders).
Handling Hard vs. Soft Bounces
When an email cannot be delivered, it "bounces." Understanding the difference between these two categories is critical for maintaining your cold email deliverability.
- Hard Bounces: These are permanent delivery failures. They occur when an email address does not exist, the domain is invalid, or the recipient’s mail server has blocked your IP permanently.
- Action: You must remove hard bounces from your list immediately. Most modern email infrastructure platforms, including Mission Inbox, handle this automatically to protect your reputation.
- Soft Bounces: These are temporary delivery failures. They happen when a recipient's inbox is full, the server is temporarily down, or the message size is too large.
- Action: You can attempt to resend to these addresses. However, if an address soft-bounces more than three times in a row, it should be treated as a hard bounce and removed.
The Role of Email Verification Software
Before you even hit "send," you should validate your list using email verification software. These tools perform several technical checks without actually sending an email:
- Syntax Check: Ensures the email follows the correct format (e.g., no missing "@" symbols or invalid characters).
- MX Record Verification: Confirms that the domain actually has a functioning mail server.
- Catch-All Detection: Identifies domains that accept all emails sent to them, which are riskier for deliverability.
- Disposable Email Detection: Flags temporary addresses often used by users to bypass sign-up forms.
Using a verification tool reduces your initial bounce rate, which is vital when you are starting with a new IP or domain.
Determining Cleaning Frequency
How often you clean your list depends on your sending volume and how quickly your data decays.
- High-Volume Senders (Daily): If you are sending tens of thousands of emails daily, list hygiene should be an automated, real-time process integrated into your email infrastructure.
- Moderate Senders (Monthly): For typical B2B outreach or newsletters, a deep scrub once a month is usually sufficient.
- Low-Volume Senders (Quarterly): Even at low volumes, email data "decays" at a rate of about 22% per year. Clean your list at least every 90 days to stay ahead of stale data.
Optimizing Content and Sending Patterns
Effective email deliverability isn't just about technical setup; it’s about how your content interacts with modern spam filters and how your sending cadence signals your legitimacy to Internet Service Providers (ISPs). To maintain high inbox placement, you must optimize every element of your message for both the recipient and the automated gatekeepers.
Crafting Spam-Resistant Subject Lines
Subject lines are the first thing both recipients and Bayesian filters analyze. While marketing appeal matters, your primary goal is to avoid triggering automated spam defenses. These filters use statistical models to assign a "spam score" based on the presence of high-risk keywords and formatting.
To keep your subject lines clean, follow these technical guidelines:
- Avoid Filter Triggers: Words like "Free," "Guaranteed," "Urgent," or "Cash" are high-correlation markers for spam and phishing.
- Match Subject to Body: ISPs look for consistency. If your subject line promises a "Project Update" but the body is a promotional offer, it triggers deceptive intent filters, which can lead to immediate blacklisting.
- Limit Special Characters: Overuse of emojis, all-caps, or strings of punctuation (??!!$$) increases your spam score. Filters interpret these as attempts to bypass standard text analysis.
The Impact of Personalization on Inbox Placement
Personalization is a powerful lever for sender reputation. From a deliverability perspective, every positive interaction—like a reply or a move from the "Promotions" tab to the "Primary" inbox—acts as a deposit into your reputation bank.
When you use dynamic tags (like first names or company-specific references), you create a unique content fingerprint for every message. This is critical because:
- Hash-Busting: Filters often look for identical templates sent to thousands of recipients. By personalizing the text, you ensure that the cryptographic "hash" of each email is different, preventing filters from identifying your campaign as a massive, automated blast.
- Positive Engagement Signals: High open and reply rates generated by personalized content tell ISPs that your mail is wanted, which reinforces your domain reputation and ensures future messages stay out of the spam folder.
Balancing Text and Images
A common mistake is sending image-heavy emails. Because spam filters cannot "read" text embedded in an image as easily as standard HTML, they often view high image-to-text ratios as a tactic to hide malicious content.
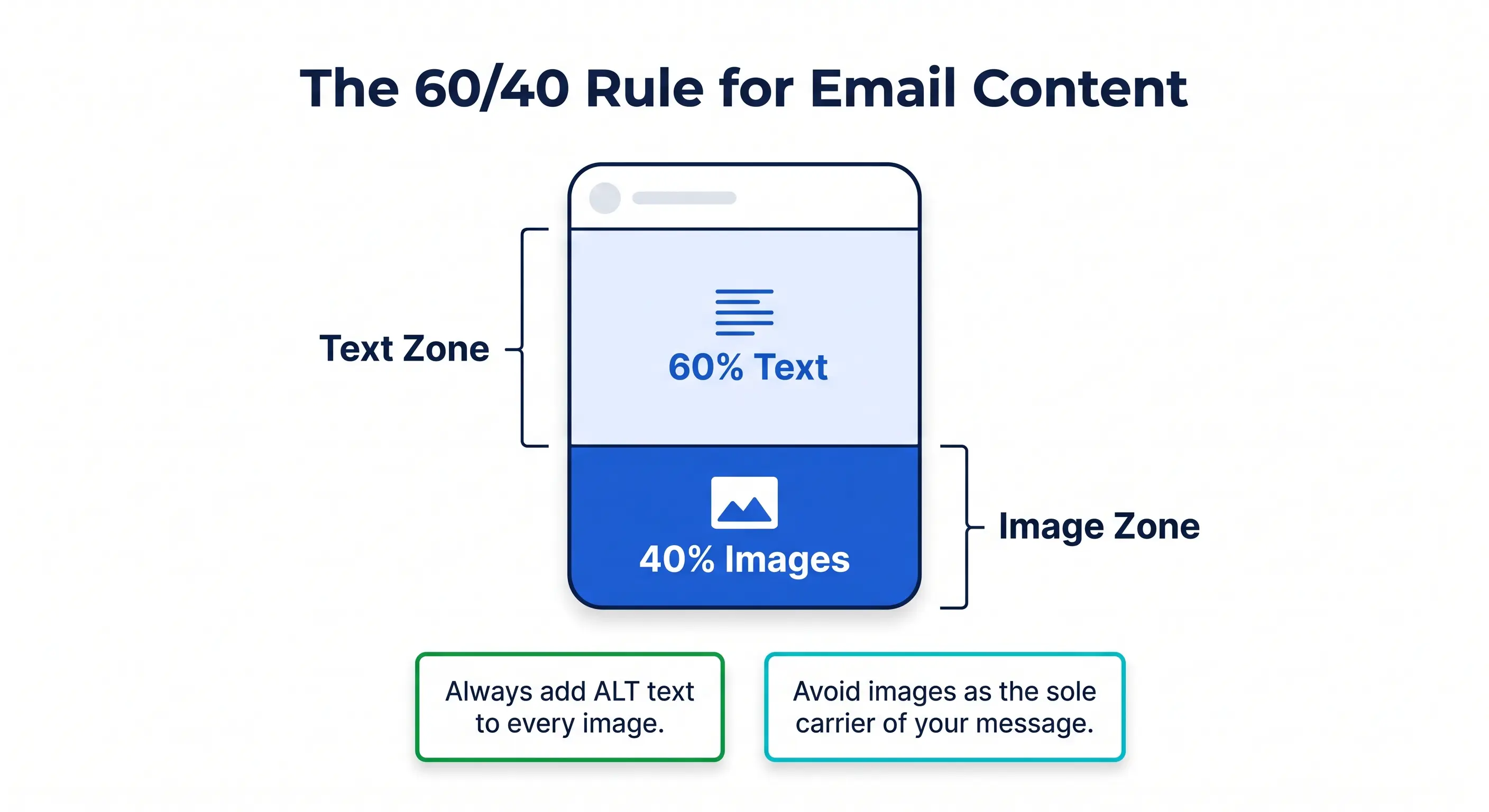
To optimize your content balance:
- Follow the 60/40 Rule: Aim for at least 60% text and no more than 40% image coverage.
- Include ALT Text: Always add descriptive ALT tags to your images. This provides context to filters and ensures accessibility for users who have images disabled.
- Avoid Large Files: High-resolution images increase the "weight" of your email. Large file sizes are often flagged as potential carriers of malware or slow-loading junk.
Frequency and Automation Best Practices
ISPs prioritize consistency above all else. Sudden spikes in volume—often referred to as "burst sending"—are a major red flag for spam activity. To protect your deliverability, your sending patterns must appear human and predictable.
- Consistent Cadence: Avoid sending 10,000 emails on a Monday and none for the rest of the week. Distribute your volume evenly to establish a steady reputation.
- Automated Warm-Up: If you are using a new domain or IP, you must utilize a premium warm-up service to gradually increase volume and build trust with mail servers.
- AI-Powered Pacing: Modern infrastructure, such as MI Shield™, uses AI to scan every outgoing message for potential triggers and automatically adjusts sending speed to stay within the limits of major providers like Google and Outlook.
- List Hygiene: Regularly purge inactive subscribers. High bounce rates and low engagement from stale lists will degrade your reputation and cause your automated sequences to fail.
Compliance and Subscription Management Standards
Compliance is often viewed as a legal hurdle, but in the world of high-volume sending, it is the bedrock of sender reputation. Maintaining strict subscription standards ensures that your emails are expected, wanted, and engaged with—all of which are critical signals to Mailbox Providers (MBPs) that your content belongs in the inbox rather than the spam folder.
Implementing a Double Opt-In Process
While single opt-in might grow a list faster, Double Opt-In (DOI) is the undisputed gold standard for email deliverability best practices. This two-step verification process requires a subscriber to click a confirmation link in a follow-up email before being added to your primary mailing list.
The benefits of DOI go far beyond mere compliance:
- Eliminates Bot Signups: It prevents "spam traps" and fake addresses from entering your database.
- Validates Intent: It ensures every subscriber actually wants your content, leading to higher engagement rates.
- Reduces Complaints: High complaint rates are the fastest way to get blacklisted; DOI virtually eliminates "I didn't sign up for this" reports.
Following the M3AAWG Sender Best Common Practices is essential for any enterprise-level sender. These guidelines emphasize that explicit, documented consent is the only way to maintain long-term access to the inbox.
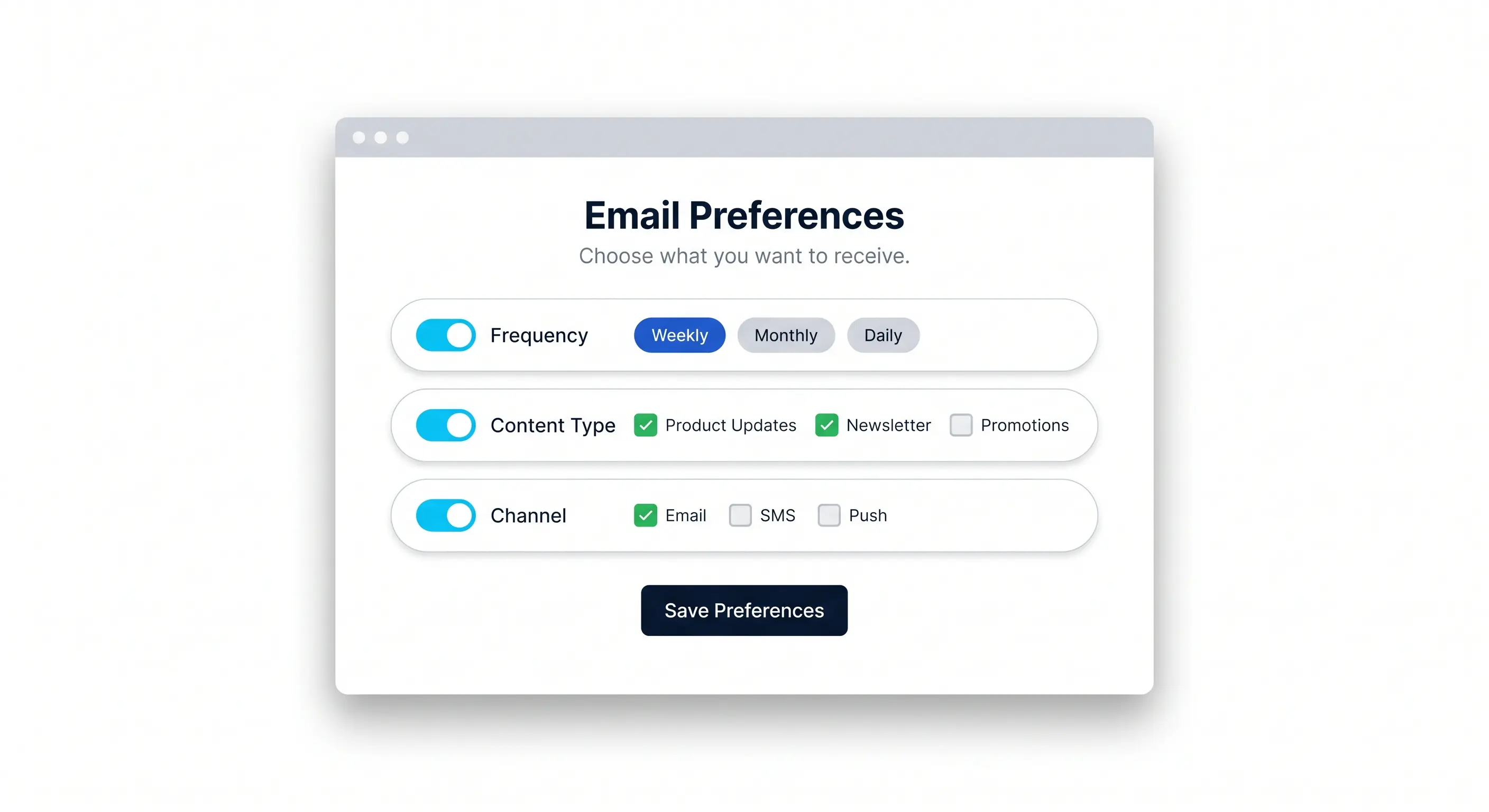
Managing Consent and Preference Centers
Consent is not a one-time event; it is an ongoing relationship. Instead of offering a binary "stay or leave" option, sophisticated senders utilize Preference Centers. This allows subscribers to customize their experience by selecting:
- Frequency: Daily, weekly, or monthly digests.
- Content Type: Product updates, newsletters, or promotional offers.
- Channels: Email, SMS, or push notifications.
By giving users control, you reduce the likelihood of a total "Unsubscribe" and protect your [sender reputation](https://knowledge.missioninbox.com/premium-warm-up-in-mission-inbox-vs.-sep-warm-up). At Mission Inbox, we emphasize that automated compliance and user-centric preference management are key to scaling your infrastructure without triggering filters.
Essential Unsubscribe Requirements
Providing a clear, easy way to opt-out is not just a courtesy—it is a legal necessity under regulations like CAN-SPAM (US), CASL (Canada), and GDPR (EU). Failing to include a functional unsubscribe mechanism can lead to heavy fines and immediate domain blacklisting.
To meet modern standards, your unsubscribe process must be:
- Visible and Easy to Find: Do not hide the link in tiny fonts or low-contrast colors.
- Single-Click (RFC 8058): Per the 2024 requirements from Google and Yahoo, bulk senders must support one-click unsubscribes in the email header to ensure a seamless user experience.
- Promptly Honored: Legally, you must process opt-out requests within 10 business days, though modern deliverability standards expect this to happen instantaneously.
If a user cannot find the unsubscribe link, they will use the "Report Spam" button instead. While an unsubscribe simply removes a name from your list, a spam report signals to the MBP that your entire domain may be untrustworthy. Always make the exit as easy as the entrance to keep your deliverability metrics healthy.
Monitoring and Maintaining Email Health
Effective email deliverability best practices require more than just a one-time setup; they demand continuous oversight. For high-volume senders, email health is a moving target influenced by changing ISP algorithms, recipient behavior, and technical performance. Maintaining a "clean" sending profile ensures that your infrastructure remains trusted by major mailbox providers (MBPs).
Key Tools for Deliverability Monitoring
To maintain high deliverability, you must leverage authoritative tools that provide direct insight into how your emails are perceived by the receiving end. These tools generally fall into three categories:
- Postmaster Dashboards: These are provided by the ISPs themselves. Google Postmaster Tools is essential for tracking your reputation with Gmail users, providing data on spam rates, domain reputation, and IP reputation. Similarly, Microsoft SNDS (Smart Network Data Services) offers data on how many "complaint" reports your IPs are generating within the Outlook/Hotmail ecosystem.
- Reputation Lookups: Third-party security databases track global sending behavior. Authoritative sources include Cisco Talos and Barracuda Central. Checking these regularly helps you identify if your IP or domain has been flagged for suspicious activity across the broader web.
- Seed List Testing: This involves sending test campaigns to a "seed list" of controlled mailboxes across different providers. This helps you identify if your content is being routed to the inbox, the "Promotions" tab, or the spam folder before you send to your entire list.
Interpreting Your Email Health Score
An Email Health Score is typically a platform-specific metric provided by your Email Service Provider (ESP) or deliverability platform. This score is an aggregate of your internal performance data, including:
- Bounce Rates: The percentage of emails that could not be delivered.
- Complaint Rates: How often recipients mark your messages as spam.
- Engagement Metrics: Open and click-through rates, which indicate to the platform that your content is valuable.
While a high email health score on your sending platform is a positive sign, it is important to remember that this is an internal view. It measures how well you are adhering to the platform’s specific guidelines and how your audience is reacting within that ecosystem. For a more comprehensive strategy, you can learn how to monitor and improve your email sending score to ensure your internal metrics align with external expectations.
Understanding Your Sender Reputation Score
Unlike a health score, a Sender Reputation Score is an external, global assessment of your IP address and sending domain. It is calculated by ISPs and third-party security providers to determine the "trustworthiness" of your mail.
The primary difference lies in the authority of the data:
- Platform Health Scores focus on engagement and compliance within your sending software.
- Sender Reputation Scores focus on technical signals (like DNS authentication), blocklist appearances, and historical volume patterns across the entire internet.
A "Good" reputation score at Cisco Talos or a high SenderScore (from Validity) indicates that the internet's gatekeepers view you as a legitimate sender. If your reputation score drops, even high-engagement content may be blocked at the gateway level before it ever reaches the recipient's "spam" folder.

Monitoring both internal health and external reputation ensures that you have a 360-degree view of your infrastructure's performance, allowing you to catch deliverability "hiccups" before they escalate into full-scale blocks.
The Intersection of Sending Strategy and Infrastructure Reliability
Even the most refined email deliverability best practices will underperform if they are built on a foundation of shaky infrastructure. High-volume sending requires more than just clean lists and engaging content; it demands a synergy between your sending strategy and the hardware, IP reputation, and routing logic that powers your outreach.
Reliability is the bridge between an email being sent and an email being seen. When your infrastructure is optimized, it absorbs the volatility of ISP algorithms, ensuring that your sender reputation remains stable even as you scale your operations.
Scaling Best Practices with Enterprise Infrastructure
Implementing best practices manually becomes unsustainable as your volume grows. To maintain high placement rates, you need an enterprise-grade email deliverability platform that automates the technical complexities of volume management.
At Mission Inbox, we bridge the gap between strategy and execution by providing:
- Dedicated IP Allocation: Removing the risks associated with shared "noisy neighbor" environments to give you full control over your reputation.
- AI-Powered Protection: Proactive monitoring that identifies potential delivery bottlenecks before they result in bounces or blacklisting.
- Seamless Scalability: Infrastructure designed to handle sudden spikes in volume without triggering ISP rate limits or throttling.
By aligning your strategic goals with a robust technical foundation, you ensure that every message has the best possible chance of reaching the inbox. Transitioning from high-level strategy to execution requires a deep dive into the specific protocols that verify your identity to receiving servers—beginning with the essential pillars of Technical Authentication and Sender Reputation.
Email Deliverability FAQs
How long does it take to see improvements in deliverability after implementing these changes?
Improvements in inbox placement are rarely instantaneous because mailbox providers rely on long term patterns to establish sender trust. While technical authentication fixes like SPF and DKIM take effect within hours, rebuilding a damaged reputation typically requires two to four weeks of consistent, high quality sending. ISPs monitor behavior over time to ensure that improved practices are a permanent shift rather than a temporary tactic to bypass filters.
Can a single spam complaint ruin my sender reputation?
A single complaint is unlikely to ruin your standing, but it serves as a critical data point for ISP algorithms. High volume senders must maintain a complaint rate below 0.1 percent to stay in the primary inbox. If a complaint originates from a highly active user or occurs during a period of low volume, the relative impact on your sender reputation score can be more significant than a complaint in a larger, more engaged pool.
What is the difference between a global blacklist and a local filter?
Global blacklists are third party databases such as Spamhaus that many providers use to block suspicious traffic across the entire internet. In contrast, local filters are internal mechanisms used by specific providers like Gmail or Yahoo to evaluate mail based on their own users' interactions and history. You can have a clean record on every public blacklist and still suffer from poor deliverability if a specific provider's local filters identify your content as irrelevant to their subscribers.
Does the time of day I send emails impact my deliverability rate?
The timing of your campaigns influences deliverability through its direct impact on user engagement metrics. When you send messages during windows when your audience is most likely to open and interact, you generate the positive signals that ISPs use to justify inbox placement. Maintaining a predictable sending schedule helps you avoid erratic volume spikes that can trigger automated security alarms, reinforcing the need for more sophisticated control over your sending environment.
Automating Infrastructure for High Volume Success
Managing the complexities of a large scale email operation requires more than just manual checklists. Transitioning to a dedicated IP infrastructure allows you to isolate your reputation from other senders while utilizing AI powered protection to maintain optimal performance. This sophisticated approach automates technical safeguards and protects your domain health, ensuring that your messages reach the inbox even as your sending volume scales across multiple regions and providers.


